Hyperconvergence
Hyperconvergence
Hyper-converged products
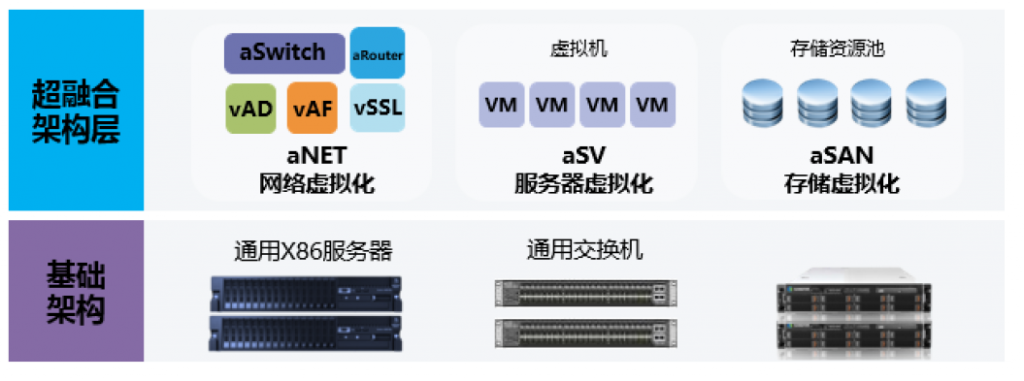
Hyper-converged architecture: Hyper-converged infrastructure is a technical architecture that uses computing, network, and storage resources as basic components, and is selected and predefined according to system requirements. The specific implementation method generally refers to the same set of units. Nodes (x86 servers) incorporate software virtualization technology (including virtualization of computing, network, storage, security, etc.), and each set of unit nodes can be aggregated through the network to achieve modular seamless scale-out expansion (scale-out). ) To build a unified resource pool.
The core value brought by hyper-converged architecture
Reliability: The hyper-converged architecture uses software to define the data center to form a large resource pool for computing, storage, and network security, which can flexibly and quickly build the business system in the data center, and also adopts a variety of technologies as the business system Provide reliability guarantee.
Security: The hyper-converged architecture also provides a guarantee for the security of the customer’s business system. From the virtualization host level, it provides customers with virtual machine disk data encryption. At the same time, based on the virtual firewall function in the virtual network, L2-L7 three-dimensional security protection is provided for the virtual machine to ensure the security of the business system.
Flexibility: The hyper-converged architecture adopts a distributed scale-out architecture design. When the business system needs to be expanded and upgraded, the corresponding server computing nodes need to be added, and the linear increase in capacity and performance can be achieved.
Value-added service products:
1.SSL Video: Encrypted video
Encryption technology makes video transmission more secure and private.
2.
Office Firewall: firewall
Through the two-way analysis of the network layer and application layer,
it provides more powerful security protection capabilities than traditional
firewall deployment.
3.
Cloud security monitoring
From the physical environment, basic equipment, network security, to
ensure the safe operation of business systems and the privacy of customer data.
4.
Media Cloud
Based on real-time stream distributed distribution technology,
decentralized transcoding technology, virtual live broadcast, video intelligent
recognition technology, to achieve fast and efficient transcoding and other
functions.
5.Voip: Internet phone
Using the latest IP technology as the communication protocol, you can
enjoy free communication for intra-network inter-dial multi-person conferences.
6.GAFs
cloud storage
The use of a distributed archive storage system strictly guarantees the
security of data storage and the high availability of services.
7.
Wifi Cloud Internet behavior management
With professional behavior management, application management, flow control and management, information management, illegal hotspot management, behavior analysis, wireless network management, unified Internet behavior management.
